Wearable health devices are revolutionizing healthcare but also exposing sensitive data to cyber threats. With over 40 million patient records breached annually in the U.S. and healthcare data breaches costing an average of $10.93 million in 2023, robust encryption is essential to protect personal health information.
Key Takeaways:
- Why Encryption Matters: Encryption safeguards sensitive data like heart rate, sleep patterns, and glucose levels from cybercriminals and ensures compliance with regulations like HIPAA.
- Main Challenges: Wearable devices often face outdated software, weak credentials, and vulnerabilities in data transit, which account for over 60% of healthcare data breaches.
- Encryption Standards: AES-256 for data at rest and TLS for data in transit are widely used. Emerging methods like Quantum Key Distribution (QKD) and Format-Preserving Encryption (FPE) are gaining traction.
- Symmetric vs. Asymmetric Encryption: Symmetric encryption (e.g., AES) is faster and ideal for resource-limited devices, while asymmetric encryption (e.g., RSA, ECC) offers stronger security but requires more processing power.
Quick Comparison:
| Feature | Symmetric Encryption (AES) | Asymmetric Encryption (RSA/ECC) |
|---|---|---|
| Key Structure | Single secret key | Public and private key pair |
| Speed | Faster | Slower |
| Security | Lower if key is exposed | Higher due to key separation |
| Best Use Case | Large data volumes | Small data or key exchanges |
Encryption, combined with AI-driven threat detection, Zero Trust architectures, and blockchain, is paving the way for a more secure future in wearable health technology. Protecting sensitive health data is critical as the global wearable medical devices market is projected to exceed $40 billion by 2027.
Every Byte Matters: Traffic Analysis of BluetoothWearable Devices
Security Challenges in Wearable and IoT Health Devices
The world of wearable health devices faces serious security challenges, with vulnerabilities making encryption both a complex and critical necessity. In 2022 alone, there were over 112 million attacks on IoT devices, highlighting the ongoing struggle to protect sensitive patient data [4]. These weaknesses not only put data at risk but also pose potential threats to patient safety. Let’s dive deeper into the common vulnerabilities and the far-reaching consequences of these security gaps.
Common Vulnerabilities in Wearable Devices
Wearable devices often fall short when it comes to robust security measures. Many rely on weak or default credentials, opening doors for cybercriminals to exploit. Encryption, a key line of defense, is frequently outdated or improperly configured, leaving sensitive information vulnerable to interception.
Another major issue is outdated software and firmware. Unlike smartphones, which benefit from regular security updates, many wearables operate on older systems that rarely receive updates, creating an expanded attack surface. Poor device configuration - such as insecure default settings and inadequate lifecycle management - further worsens the situation. For example, studies reveal that 75% of smart infusion pumps have security flaws that make them susceptible to cyberattacks [4].
Impact of Cyberattacks on Health Data
The fallout from cyberattacks on wearable health devices goes far beyond mere data theft. In 2023, healthcare data breaches cost an average of $10.93 million, an 8.22% increase from the previous year [7]. When patient data is compromised, it can lead to identity theft, financial fraud, and even blackmail [6]. Worse still, tampered data can mislead diagnoses and treatment decisions [5].
High-profile breaches paint a troubling picture. In July 2023, a breach exposed the data of 11 million patients, leading to widespread concerns over identity theft and fraud [6]. Similarly, a 2021 cyberattack on a California healthcare provider forced IT systems offline, pushing the organization to rely on manual processes. This disruption increased hospital wait times by 47.6% and resulted in nearly $120 million in losses [6]. Globally, cybercriminals targeted a Spanish university hospital in March 2023, stealing over 4 terabytes of data, including patient and clinical trial information. When a $4.5 million ransom went unpaid, the stolen data was leaked on the dark web [6].
The numbers are staggering: 92% of healthcare organizations reported at least one cyberattack in the past year, and 66% of patients said they would consider switching providers if their personal data were compromised [7]. These incidents highlight the urgent need for stronger security measures, including emerging lightweight encryption protocols.
Regulatory and Operational Barriers
Efforts to improve encryption face hurdles from inconsistent protocols, forcing manufacturers to adopt patchy and often inadequate security measures. These regulatory and operational barriers make it harder to implement effective encryption strategies. This includes preparing for future threats with post-quantum cryptography.
Low user awareness adds another layer of risk. Operational challenges - like compatibility issues, fears of disrupting patient care, and the difficulty of integrating various device types - often delay crucial updates, leaving systems vulnerable [1]. Cost is another major factor; healthcare organizations must juggle the need for advanced security features with tight budgets. Managing device security throughout its lifecycle is no easy task, especially when questions about data ownership and regulatory oversight remain unresolved.
Encryption Standards for Wearable Health Devices
Encryption standards play a critical role in protecting sensitive health data, whether it's being transmitted or stored. Given the vulnerabilities previously discussed, these standards are essential for maintaining the security of personal health information. They serve as the foundation for secure health data management, ensuring protection at every stage of its lifecycle. Let’s explore how encryption applies to different states of data and the protocols that strengthen wearable device security.
Encryption for Data in Transit and at Rest
Understanding the difference between data in transit and data at rest is key to implementing effective security measures. Data in transit refers to information actively moving between locations, such as from a wearable device to a healthcare system. In contrast, data at rest is stored information, whether on a device, server, or cloud network [12].
Data in transit faces specific risks as it moves across networks. In fact, over 60% of healthcare data breaches involve intercepted data in transit [1]. To mitigate these risks, healthcare organizations rely on encrypted connections like HTTPS, SSL, and TLS. Among these, the Transport Layer Security (TLS) protocol has emerged as a trusted standard for securing data exchanges between wearable devices and healthcare systems.
On the other hand, data at rest demands a different set of protections. According to HIPAA guidelines, encryption methods such as AES-256 are highly recommended for safeguarding stored health information [9]. This ensures that even if unauthorized access occurs, the encrypted data remains unreadable. While data in transit is often seen as more vulnerable [13], stored data can also be a prime target for attackers [12]. Developers can enhance security by validating server certificates, applying SSL/TLS encryption for transmissions, and encrypting sensitive files or storage systems for data at rest [11][12].
Role of Standardized Security Protocols
Unified security practices depend heavily on industry standards, which help streamline protections across the wearable health ecosystem. For structured health data, Format-Preserving Encryption (FPE) is especially effective, as it secures the data without altering its original format [10]. Additionally, token-based access controls play a crucial role in encrypting critical API data, such as tokens and keys, ensuring that only authorized users can access sensitive information [11].
Emerging technologies like Quantum Key Distribution (QKD) are beginning to influence wearable device security. QKD offers a method of communication that is theoretically resistant to quantum computing attacks, providing a glimpse into the future of encryption [10]. Beyond encryption, strategies like Data Loss Prevention (DLP) add extra layers of security. DLP measures include disabling copy-and-paste functions, blocking screen recording, and limiting application screen sharing. Network security tools, such as firewalls and access control systems, further reinforce the protection of data in transit [11][12].
EHR Integration and Wearable Ecosystems
Integrating wearable devices with Electronic Health Records (EHRs) presents unique encryption challenges. HIPAA regulations require distinct security measures for data in transit and data at rest [9], which means every step of the data exchange process must be secure. For example, when a fitness tracker uploads heart rate data, that information needs to remain encrypted during transmission, temporary cloud storage, and its final integration into the EHR system.
In a 2023 study, researchers from ESET revealed vulnerabilities in popular fitness trackers. They demonstrated how attackers could manipulate devices to alter health data, including step counts and heart rate readings [1]. This highlights the importance of real-time end-to-end encryption in wearable–EHR ecosystems, where both the integrity and privacy of data must be preserved.
Wearable devices generate a wide variety of data, from biometric and activity metrics to environmental information. Encryption protocols must adapt to handle this diversity while ensuring smooth integration with structured EHR systems. To address these challenges, healthcare organizations are increasingly adopting systematic data classification policies. These policies ensure that appropriate security measures are applied to data at rest, enhancing protection across interconnected wearable ecosystems [12]. As the landscape evolves, comparing symmetric and asymmetric encryption methods becomes even more critical in determining their practical applications.
Symmetric vs. Asymmetric Encryption for Wearable Devices
When it comes to securing wearable health devices, choosing the right encryption method is a balancing act between efficiency and security. The two main options - symmetric and asymmetric encryption - each come with distinct strengths, which play a big role in deciding their suitability for devices with limited resources.
Comparing Encryption Methods
The key difference between symmetric and asymmetric encryption lies in how they handle keys. Symmetric encryption relies on a single secret key, making it faster and less demanding on computational resources. Asymmetric encryption, on the other hand, uses a pair of keys (a public key and a private key), offering stronger security but at the cost of higher computational requirements. For instance, symmetric algorithms like AES are much faster and more efficient than asymmetric ones like RSA, which is a critical factor when encrypting data frequently on resource-constrained devices.
Here’s a quick comparison of the two methods:
| Feature | Symmetric Encryption | Asymmetric Encryption |
|---|---|---|
| Key Structure | Single secret key | Public and private key pair |
| Processing Speed | Faster | Slower |
| Security Level | Lower if the key is compromised | Higher due to key separation |
| Key Distribution | Requires a secure channel | No secure channel needed |
| Best for Data Size | Large amounts of data | Smaller amounts of data |
| Implementation | Simpler | More complex |
Building on this, asymmetric methods like Elliptic Curve Cryptography (ECC) strike a promising balance between security and efficiency, especially for wearables. For example, AES-256 is widely used for symmetric encryption to protect classified data, while RSA 2048 is a common choice for asymmetric encryption [14]. ECC offers similar security to RSA but uses much shorter key lengths - like 256, 384, or 521 bits - making it an excellent choice for devices that need strong security without overloading their processors [10].
Research Insights on Encryption for Wearables
Understanding the strengths and weaknesses of these encryption methods is key to tackling the specific wearable health data security challenges. Research shows that the choice of encryption often depends on the device's capabilities and intended use [10]. For example, advanced smartwatches with more processing power frequently use AES because it’s both secure and efficient [10]. In contrast, basic fitness trackers, which have limited resources, may struggle to handle computationally heavy algorithms like RSA. A combination of ECC and AES can provide an ideal mix of security and efficiency for these devices [10].
The importance of effective encryption goes beyond just protecting data - it can also save money. Data breaches can cost companies over $240,000, making robust encryption a worthwhile investment [15]. This is especially relevant as the global wearable medical devices market is expected to surpass $40 billion by 2027 [1].
From a technical standpoint, time complexity analyses further highlight these differences. AES operates with O(n) complexity for both encryption and decryption, making it well-suited for continuous data streams. This efficiency is vital for real-time data sync in health monitoring. In contrast, RSA's encryption and decryption complexities - O(n²) and O(n³), respectively - make it less practical for real-time applications [10].
Additional techniques, like Format-Preserving Encryption (FPE), can enhance security while maintaining the data’s structure, and emerging methods such as Quantum Key Distribution (QKD) promise secure communication that could withstand quantum computing threats [10].
sbb-itb-f5765c6
Future Directions and Integration with AI Platforms
The landscape of wearable health data protection is undergoing a major transformation, thanks to advancements in AI and encryption. With the AI healthcare market projected to grow from $10.4 billion in 2021 to an estimated $120.2 billion by 2028, the need for integrating smart security systems into health platforms has never been more pressing [17]. This shift is paving the way for AI-powered solutions to seamlessly integrate with unified health data platforms.
AI-Driven Threat Detection and Monitoring
Artificial intelligence is redefining cybersecurity by moving it from a reactive approach to a proactive one. Mohammed Rizvi highlights this shift: "Due to its ability to evaluate security threats in real-time and take appropriate action, artificial intelligence has emerged as a key component of cyber security" [16].
AI now powers real-time monitoring systems that analyze data flows from wearable devices, identifying anomalies that could indicate potential cyber attacks. Charles Cinert, Chief Services Officer at ClearDATA, underscores this importance: "Real-time monitoring and threat detection are essential for identifying suspicious activity" [1].
The financial benefits are equally noteworthy - AI-driven threat detection can save organizations an average of $1.4 million per attack. This becomes even more critical when considering that over 60% of healthcare data breaches involve data in transit, as highlighted in a 2024 Ponemon Institute report [1][3].
AI is also transforming compliance monitoring by automating the enforcement of regulations like HIPAA. This reduces the risk of human error while improving operational efficiency. Platforms like BondMCP are leveraging these advancements to deliver comprehensive data security solutions.
The Role of BondMCP in Secure Data Exchange
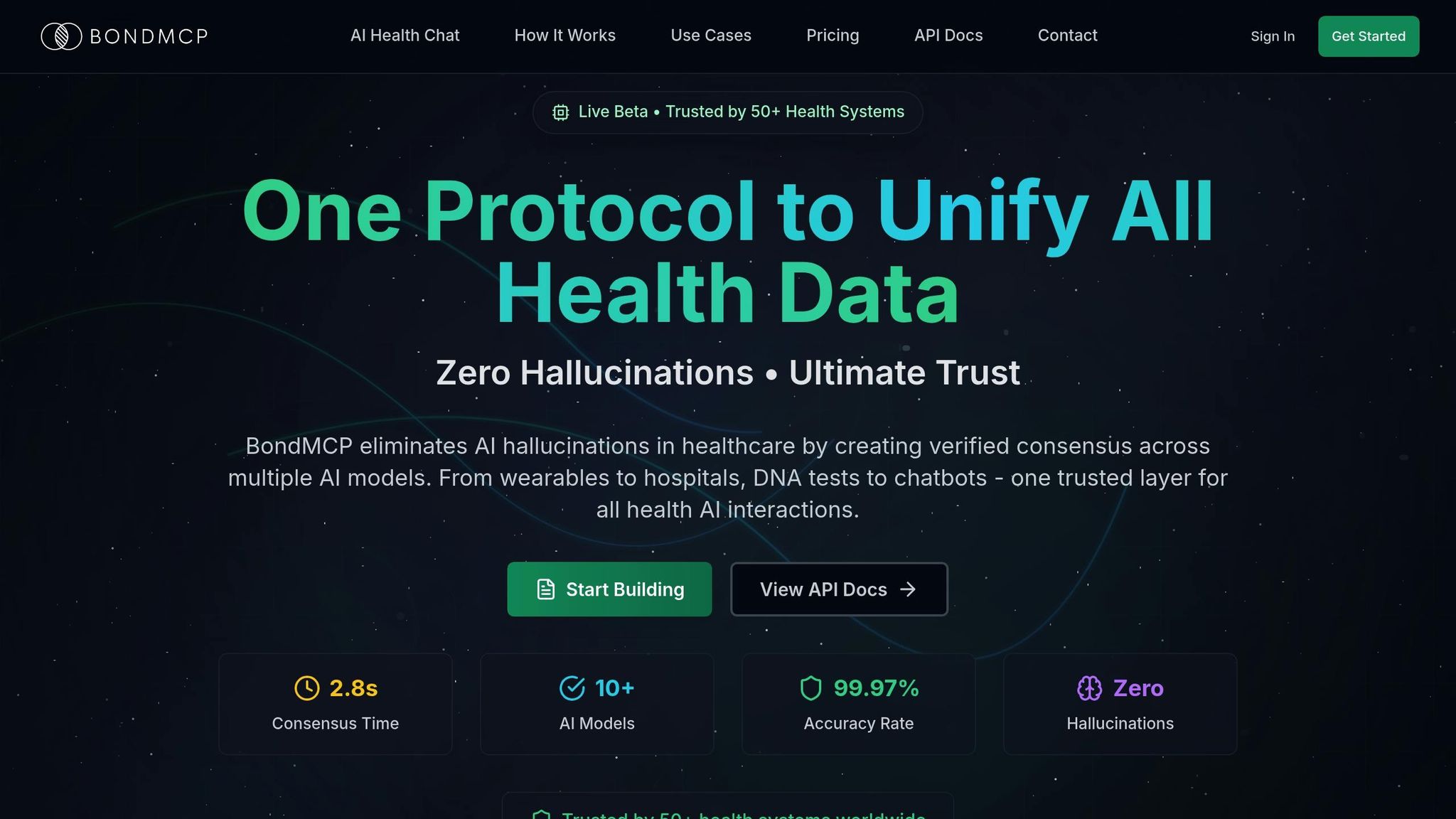
BondMCP tackles the challenges of data fragmentation and security vulnerabilities by building on established encryption standards. Traditional health platforms often create weak points at connection interfaces, but BondMCP addresses this by unifying data exchange through encrypted, standardized channels. This reduces development complexity and minimizes security risks.
For example, when your sleep tracker communicates with a training coach app or when lab results update your supplement regimen, BondMCP ensures these exchanges occur securely through its structured protocol. By eliminating the risks associated with disconnected data pathways, the platform provides a streamlined and secure system for data exchange.
Healthcare organizations can also use BondMCP's multi-layered security framework to integrate siloed data while maintaining strict access controls. Its AI agents work collaboratively to optimize health outcomes, continuously monitoring and protecting sensitive information against threats.
Advancements in Health Data Encryption
Encryption technologies are advancing rapidly, incorporating Zero Trust architectures and smarter identity verification systems. Trea Zemaitis, Senior Security Engineer at Core4ce, explains: "By requiring strict identity verification, granular access controls, and continuous monitoring, Zero Trust ensures that even if an IoMT device is compromised, the broader network remains protected" [19].
Wearable devices are increasingly adopting multi-factor authentication and biometric verification as standard security measures. With 90% of hospitals expected to use AI for early diagnosis and remote monitoring by 2025, these protections are becoming essential [18].
AI also enhances the interpretation of physiological sensor data. Machine learning algorithms now enable more accurate signal processing, while energy-efficient routing algorithms use reinforcement learning to optimize network pathways based on real-time energy needs [20].
Another exciting development is predictive maintenance. AI models can now anticipate sensor failures before they happen, and dynamic algorithms adjust bandwidth and power usage in real time to prevent disruptions [20].
The combination of AI and blockchain technologies is unlocking new possibilities for secure health data transmission. These systems ensure patient information is shared between devices and platforms without unauthorized access. At the same time, AI algorithms anonymize data for research, preserving privacy [16].
Conclusion
The growing integration of wearable health devices into healthcare systems highlights an urgent need for strong security measures. As these technologies become more widespread, ensuring the protection of sensitive health data is more critical than ever.
Key Takeaways
Encryption plays a fundamental role in protecting the integrity and confidentiality of data processed by wearable devices [10]. Manufacturers must carefully select encryption algorithms. Symmetric encryption methods like AES and ECC are often favored for their balance of security and efficiency, ranking among the top 5 energy-efficient encryption methods for wearables. ECC, in particular, offers the same security level as RSA but with significantly shorter key lengths [10]. Additionally, lightweight cryptography (LWC) is emerging as a practical solution, reducing computational demands while maintaining robust security for resource-constrained devices [21].
The importance of rigorous security testing cannot be overstated. With over 10.54 million IoT-related attacks reported in December 2022 alone, implementing comprehensive testing protocols is essential [22].
Platforms such as BondMCP are addressing interoperability challenges by providing unified systems that securely manage health data across various devices and applications. These advancements not only enhance security but also facilitate seamless integration. Looking ahead, the focus shifts to emerging technologies and trends that will further shape the security landscape.
The Future of Secure Health Data
While current encryption methods form a strong foundation, the future brings both new challenges and opportunities. Quantum computing, for instance, poses a potential threat to existing encryption standards but also opens the door to innovative cryptographic solutions [10]. AI-driven threat detection is becoming increasingly advanced, with real-time monitoring systems capable of spotting anomalies that could signal cyberattacks [1]. Meanwhile, the adoption of Zero Trust architectures and multi-factor authentication ensures that even if a device is compromised, the broader healthcare network remains secure [19].
Collaboration among healthcare stakeholders is essential to establish industry-wide security standards that safeguard patient data and privacy [1]. Regulatory bodies like the FDA are also stepping up, with evolving security requirements for medical devices highlighting the push for stronger protections [8]. Moreover, the integration of blockchain technology and advanced encryption methods promises to create even more secure frameworks for transmitting health data [8].
With healthcare generating approximately 30% of the world’s data and over 40 million patient records breached annually in the U.S. alone [2], the need for robust encryption has never been more urgent. Protecting sensitive health data will require ongoing innovation, cooperation, and a steadfast commitment to security. The future depends on our ability to stay ahead of evolving threats while maintaining trust in the devices that increasingly shape modern healthcare.
FAQs
What are the key encryption challenges for wearable health devices, and how can they be resolved?
Wearable health devices bring their own set of encryption challenges, largely stemming from their compact design, limited processing power, and varied environments in which they are used. These devices frequently handle sensitive health data and rely on wireless transmission, making data integrity and device authentication particularly tricky. Their dynamic usage settings can also leave them open to risks like tampering or unauthorized access.
To address these challenges, lightweight encryption algorithms offer a way to secure data without straining the device's resources. Adding digital signatures ensures the authenticity of the data being transmitted, while technologies such as blockchain create a tamper-resistant method for storing and sharing health records. By integrating these solutions, wearables can achieve robust security while maintaining smooth performance and a seamless user experience.
How does Quantum Key Distribution (QKD) improve the security of wearable health devices compared to traditional encryption methods?
Quantum Key Distribution (QKD) and Wearable Health Device Security
Quantum Key Distribution (QKD) brings a groundbreaking approach to securing wearable health devices by leveraging quantum mechanics to exchange encryption keys in a highly secure manner. Unlike traditional encryption methods that depend on intricate mathematical algorithms - and may one day be at risk from quantum computing - QKD operates on the principle that any attempt to intercept the encryption key will disturb its quantum state. This disruption immediately alerts the involved parties, making QKD exceptionally resilient to eavesdropping and ensuring security rooted in the laws of physics.
While established encryption protocols like AES and ECC remain critical for safeguarding health data, QKD adds an extra shield against the constantly evolving world of cyber threats. When paired with traditional encryption, QKD enhances the overall security framework, enabling wearable devices to transmit sensitive health information securely, even as the threat landscape continues to shift.
How does AI enhance the security of data from wearable health devices, and how does it work with encryption protocols?
AI plays a key role in boosting the security of data collected by wearable health devices. By enabling smarter encryption methods and real-time threat detection, AI ensures sensitive information stays protected. For instance, AI can encrypt data directly on the device before it's transmitted, safeguarding it even if someone intercepts it during transfer.
AI also keeps an eye on data patterns, identifying and addressing potential security threats as they arise. When paired with encryption protocols like AES (Advanced Encryption Standard), AI not only automates but also enhances the encryption process, ensuring that unauthorized users can't access the data. This blend of advanced encryption and ongoing monitoring creates a stronger shield against cyber risks, making wearable health devices a safer and more dependable choice.
